sqlmap
The definitive open-source SQL injection detection and exploitation tool, supporting 30+ database management systems and six injection techniques.
Developer
Bernardo Damele & Miroslav Stampar
description Technical Dossier
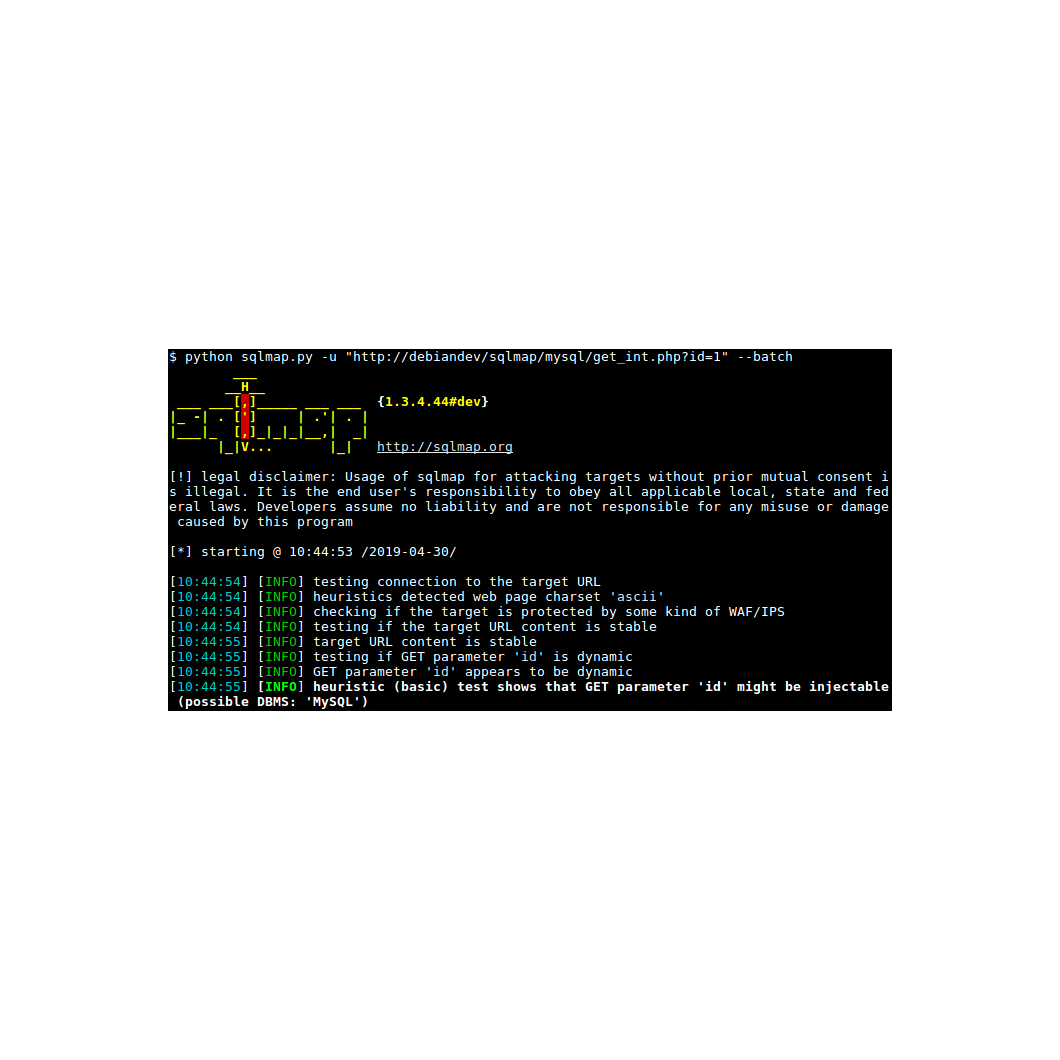
sqlmap is an open-source command-line penetration testing tool that fully automates the process of discovering and exploiting SQL injection vulnerabilities. Given a target URL or request file, sqlmap probes HTTP parameters — including GET/POST fields, cookies, and HTTP headers — injecting crafted payloads and analyzing application responses to determine exploitability. It employs six distinct injection techniques, ranging from straightforward UNION-based extraction to slower but broadly applicable boolean-based blind and time-based blind methods, adapting automatically to whichever technique works against the target.
Once a vulnerability is confirmed, sqlmap transitions into an exploitation phase capable of fingerprinting the exact DBMS version, enumerating the full database schema, and extracting arbitrary data. Advanced modules can crack extracted password hashes using a dictionary attack, read and write files on the database server’s filesystem, and — against permissive configurations — execute arbitrary OS commands through user-defined functions or xp_cmdshell. Out-of-band channels allow the tool to establish reverse shells and Meterpreter sessions independent of the HTTP response channel, making it effective even in blind scenarios with no visible output.
sqlmap is widely regarded as the definitive open-source SQL injection framework and ships as a standard tool in Kali Linux and other security-focused distributions. It integrates with both Metasploit and w3af, supports resumable sessions, and can parse raw HTTP request files exported from Burp Suite or ZAP — making it a routine component of professional web application penetration tests. Its consistent development since 2006 and coverage of OWASP’s historically top-ranked vulnerability class make it the reference implementation for SQL injection testing tooling.
layers Six Injection Techniques
Supports boolean-based blind, time-based blind, error-based, UNION query, stacked queries, and out-of-band injection covering virtually every SQL injection vector.
storage Broad Database Coverage
Fingerprints and exploits 30+ DBMS targets including MySQL, PostgreSQL, Oracle, MSSQL, SQLite, MariaDB, MongoDB, Amazon Redshift, and ClickHouse.
key Enumeration & Credential Cracking
Automatically enumerates databases, tables, columns, users, and privileges. Extracts password hashes with built-in dictionary-based cracking.
terminal OS-Level Takeover
Uploads and downloads files, executes OS commands, and establishes interactive shells or Meterpreter sessions via out-of-band TCP connections.
Distribution Model
Open Source
Free community edition available.
Enterprise support on request.
DBMS Targets
30+
Injection Types
6 TECHNIQUES
Language
PYTHON
License
GPL V2+